Preemptive cyber defenses are no longer a luxury for modern enterprises; they are a necessity. As cyber threats evolve from simple malware to sophisticated, AI-driven attacks, relying solely on reactive measures—like firewalls and antivirus software—is insufficient. To truly secure your digital infrastructure in 2026, you must shift your strategy “left of boom,” neutralizing threats before they ever strike your network.
In this guide, we will explore how to implement preemptive cyber defenses effectively, transforming your security posture from a passive shield into an active, anticipatory force.
What Are Preemptive Cyber Defenses?
Preemptive cyber defenses refer to a proactive methodology aimed at identifying, disrupting, and neutralizing threats before they can execute an attack. Unlike reactive security, which responds only after an alert is triggered or data is lost, preemptive strategies focus on predictive analysis, threat hunting, and hardening the attack surface to make successful breaches mathematically improbable.
To understand the specific risks driving this need, read our detailed report on AI Cybersecurity Threats & Defenses in 2026.
Core Pillars of a Preemptive Cyber Defense Strategy

To successfully deploy preemptive cyber defenses, you must build your strategy around three core pillars: comprehensive visibility, active deception, and continuous validation.
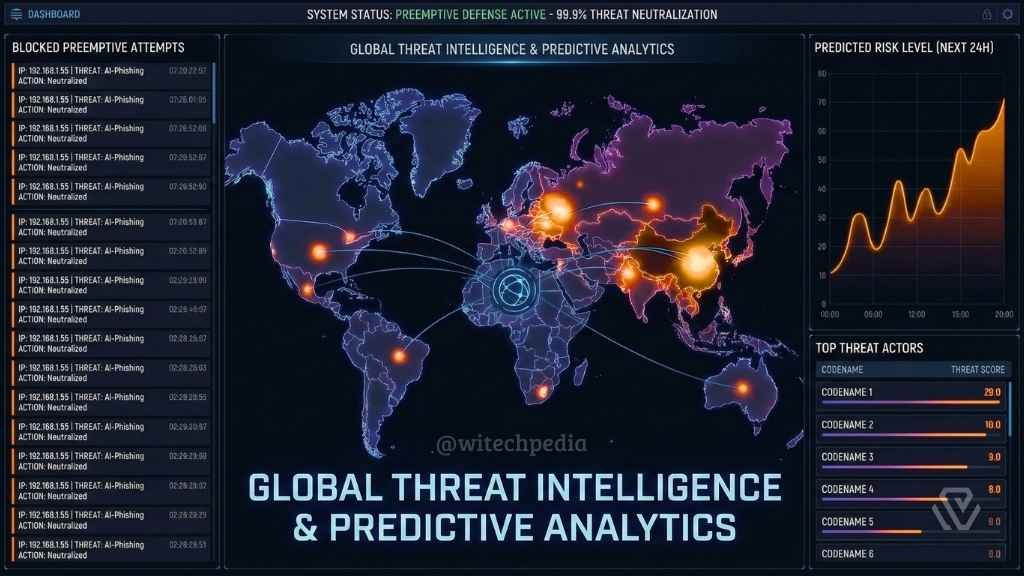
1. Threat Intelligence and Predictive Analysis
A robust preemptive cyber defense strategy starts with knowing your enemy. You cannot prevent an attack you don’t see coming. Integrating automated threat intelligence feeds allows your security operations center (SOC) to ingest real-time data regarding global attack trends.
Actionable Step:
Utilize frameworks like MITRE ATT&CK to map adversary behaviors and anticipate their next move based on global data.
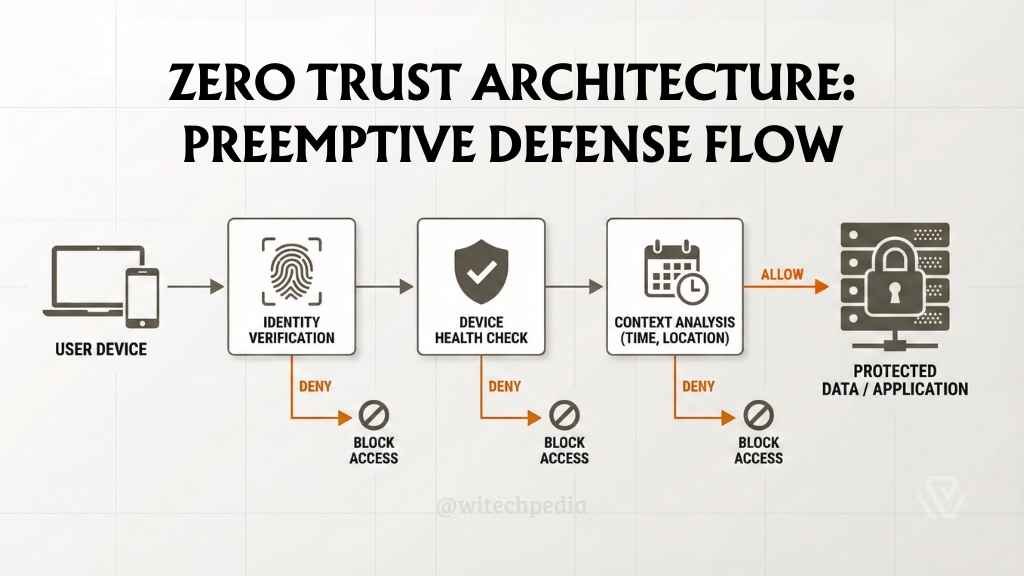
2. Zero Trust Architecture (ZTA)
The foundation of preemptive cyber defenses is the assumption that the network is already compromised. Zero Trust eliminates implicit trust by continuously validating every stage of a digital interaction. This limits the “blast radius” of any potential intrusion.
For federal standards on implementation, review the NIST Zero Trust Architecture guidelines.
3. Deception Technology
One of the most aggressive forms of preemptive cyber defense is the use of deception technology. By deploying decoys, honeytokens, and fake credentials, you can confuse attackers and detect their presence during the reconnaissance phase.
If you are building autonomous systems to handle these defenses, ensuring they are secure is vital. See our guide on How to Build Agentic AI to understand how autonomous agents interact with your network layers.
Step-by-Step: How to Implement Preemptive Cyber Defenses
Implementing preemptive cyber defenses requires a structured approach. Follow these steps to transition from reactive to proactive security.
Step 1: Conduct a Comprehensive Attack Surface Analysis
You cannot protect what you do not know exists. Preemptive cyber defenses begin with a total audit of your digital footprint, including shadow IT, forgotten subdomains, and exposed APIs.
- Tool Tip: Use automated Attack Surface Management (ASM) tools to continuously scan for vulnerabilities.
Step 2: Harden Your System Configurations
Misconfigurations are the leading cause of breaches. You must rigorously apply security benchmarks to all operating systems and applications.
For Windows environments, basic troubleshooting and hardening often start at the command line. Master the 25 Essential CMD Commands Every Windows User Should Know to audit your local network connections effectively.
Step 3: Deploy AI-Driven Anomaly Detection
Static rules miss novel attacks. Modern preemptive cyber defenses utilize Machine Learning (ML) to establish a baseline of “normal” network behavior. When an entity deviates from this baseline—such as a user accessing files at 3 AM from an unusual IP—the system can preemptively block access.
To learn more about the architecture of self-hosted AI tools that can assist in data processing, check out our OpenClaw AI Wiki.
Step 4: Validate Defenses with Breach and Attack Simulation (BAS)
Don’t wait for a real hacker to test your walls. Preemptive cyber defenses must be stress-tested. automated BAS tools launch simulated attacks against your network to identify weaknesses in your defensive stack.
The Safety Net: When Prevention Fails
While preemptive cyber defenses are superior for prevention, no system is 100% impenetrable. You must have reactive measures in place for resilience.
If a breach does occur, knowing how to recover quickly is vital to business continuity. Ensure your team is trained on How to Remove Malware from Windows 10 to clean up infections effectively before restoring from backups.
The Future of Preemptive Cyber Defenses
As we move deeper into the decade, preemptive cyber defenses will become increasingly autonomous. We will see the rise of “Self-Healing Networks” where AI agents not only detect a vulnerability but patch it instantly without human intervention.
Adopting these strategies today positions your organization as a hard target, forcing cybercriminals to move on to easier, less prepared victims.